More Retail News
Co-op appoints director of property, development and estates

WH Smith hails strong performance of travel business
WH Smith has seen an uplift in half-year sales and profit following a strong performance in its travel division. In the six months to 29 February,... View ArticleView Article

Sainsbury's boosted by strength of grocery performance
Sainsbury’s was boosted by the strength of its grocery performance in the year to 2 March as its food business “fired on all cylinders”. During the... View ArticleView Article

Søstrene Grene set to open second central London store
Søstrene Grene, the Danish homewares and lifestyle brand, is to open a new store in London’s Coal Drops Yard next month. Due to launch on 10... View ArticleView Article
Hornby chairman to step down
The Hornby models and collectibles business has announced that its chairman Lyndon Davies will be stepping down from his role at the end of this month... View ArticleView Article

Decathlon expands Buy Back scheme
Decathlon has expanded its Buy Back scheme to more sporting equipment following a successful launch last year. The scheme enables customers to swap old sporting equipment... View ArticleView Article

Gear4music full year performance in line with expectations
Gear4music, the online musical instruments retailer, has delivered a full year performance in line with expectations. In a year-end trading update, the retailer said total sales... View ArticleView Article

World Retail Congress review - recognising change is ongoing
After many years of tumultuous change in the retail sector there is growing evidence that many large organisations have now got a handle on things and... View ArticleView Article

John Lewis executive finance director, Bérangère Michel, to leave the business
The John Lewis Partnership has announced that its executive finance director, Bérangère Michel, is to leave the business later this year. In a statement, the partnership... View ArticleView Article

Pret A Manger announces board changes as it ramps up international growth
Pret A Manger has made a series of board changes as it looks ahead to its next phase of international growth. These have included one of... View ArticleView Article

Mango continues US expansion with new east coast stores
Mango is continuing to expand in the US with new east coast openings in Washington and Boston. The news follows the launch of the fashion retailer’s... View ArticleView Article

B&Q launches energy saving hubs with the GMCA to boost energy efficiency
B&Q, the home improvement retailer, has launched two in-store Energy Saving Hubs in collaboration with the Greater Manchester Combined Authority (GMCA). The hubs, located at B&Q’s... View ArticleView Article

Clarks celebrates iconic style with inaugural Wallabee Day on April 26th
Clarks are excited to announce the first-ever Wallabee Day to take place every year on 26th April, encouraging its global community of wearers to share their... View ArticleView Article

Microsoft's Olaf Akkerman joins People in Retail Awards judging panel
We’re thrilled to introduce our newest judge for the People in Retail Awards: Olaf, a dynamic leader at the forefront of the UK’s tech industry. Olaf... View ArticleView Article

Dobbies appoints Robert Cook as board advisor for its restaurant business
Garden centre retailer Dobbies has appointed Robert Cook as a board advisor to support the development of its restaurant business. A former chief executive of TGI... View ArticleView Article

The Cotswold Company expands into Northern Ireland
The Cotswold Company has expanded its premium delivery service to customers in Northern Ireland as part of its strategy to strengthen its position in the UK.... View ArticleView Article

Comment: Democratising personalisation
When entering the Salon de Parfums on the sixth floor of Harrods’ Knightsbridge flagship it not only looks pretty good with its polished marble flooring but... View ArticleView Article

Primark posts strong growth in half year sales and profit
Primark has delivered 7.5% growth in half year sales to £4.5 billion as newly opened stores and last year’s selected price increases offset the impact of... View ArticleView Article

JD Sports to acquire US retailer Hibbett
JD Sports is to acquire the US sports fashion retailer Hibbett for $1.08 billion. With headquarters in Birmingham, Alabama, Hibbett has 1,169 stores in 36 states... View ArticleView Article

John Lewis joins Canopy Pack4Good initiative
In a partnership with the environmental not-for-profit Canopy, John Lewis has become the largest UK retailer to sign up to the Pack4Good initiative Signatories to the... View ArticleView Article

Understanding the challenges of mental health in retail
In recent years, there has been a surge in raising awareness regarding mental wellbeing and the negative effects of poor mental health conditions on employees’ performance.... View ArticleView Article

Nobody's Child partners with Sojo for a pop-up repair station at Carnaby Street store
Responsible fashion brand, Nobody’s Child, is excited to announce an exclusive pop-up with SOJO repair station in celebration of World Earth Day, on Saturday 27th April... View ArticleView Article

Nudea marks Earth Day with second annual sustainability report
In alignment with Earth Day, Nudea, a pioneering B Corp certified brand, has released its second annual Sustainability Report, showcasing a year of substantial progress towards... View ArticleView Article

M&S asks public to give pre-loved clothing a second life through trial of free postal donation service
Marks & Spencer has teamed up with Oxfam to help people donate their preloved clothing to the charity through a free postal donation service. The trial... View ArticleView Article

Lidl to open new London store in Fulham
Lidl is continuing its expansion in London with the opening of a new store in Fulham this summer. The supermarket said the shop on North End... View ArticleView Article

Asda sales boosted by popularity of loyalty scheme
Asda has posted a strong uplift in full year sales and profit after it benefited from around six million customers using its rewards app. In the... View ArticleView Article

H&M Home teams up with Pantone on second collection
H&M Home is to release a second collaboration with Pantone with a new brightly coloured capsule range. Presenting with the two palettes of Zesty & Fresh... View ArticleView Article

Zuber Issa close to selling stake in Asda
Zuber Issa is close to selling his £500 million stake in Asda to TDR Capital. According to a report by Bloomberg, the billionaire is now in... View ArticleView Article

New Look’s emissions targets approved by the SBTi
New Look has received approval for its emissions targets from the Science Based Targets Initiative (SBTi). The fashion retailer has a near-term target to reduce scope... View ArticleView Article

Gloucester Quays hails year of record sales as it begins 15th anniversary birthday celebrations
The Gloucester Quays outlet centre has been boosted by a year of record sales and footfall as it celebrates its 15th anniversary. In the period April... View ArticleView Article

TikTok Shop launches new 'Preowned Luxury' category
TikTok has partnered with five luxury resellers with the launch of the ‘Preowned Luxury’ category on its app. In a release, TikTok said the new offering... View ArticleView Article

The Perfume Shop and the valuable changes the brand is making to the planet
Today, World Earth Day 2024, The Perfume Shop reports its updated initiatives to support saving the environment and planet. These initiatives include the UK’s biggest perfume... View ArticleView Article
Benefit brings back 'Bold is Beautiful' charity-giving scheme
Benefit, the beauty brand renowned for its brow products and retro-glam aesthetic, has announced the return of its ‘Bold is Beautiful’ philanthropy programme this May. As... View ArticleView Article
A third of Brits admit to throwing food away solely based on the best before date
To mark Stop Food Waste Day (24th April 2024), Too Good To Go, the social impact company behind the world’s largest marketplace for surplus food, reveals... View ArticleView Article
Exploring the impactful role of employee recognition in retail
“In the retail sector, the spirit of exceptional service heavily depends on the engagement and enthusiasm of its employees. These individuals are at the frontline of... View ArticleView Article
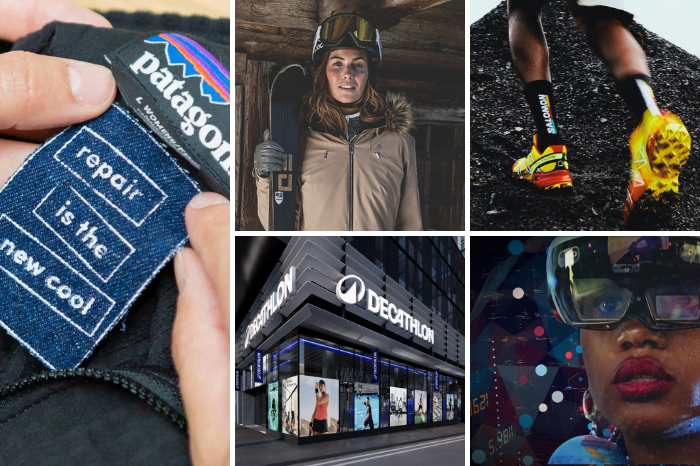
Blending boundaries: The new era of outdoor fashion and the role of technology
The evolving landscape of outdoor fashion The outdoor fashion industry is rapidly transforming, driven by a societal shift towards health and nature, fueled by the rise... View ArticleView Article

Holland Barrett invest over £4m in women's health
Holland & Barrett, the UK’s leading health and wellness retailer, is investing over £4 million into its women’s health offer, backed by a new three-year Wellness... View ArticleView Article

Fit and Sustainability in Fashion: Batch LDN
Batch LDN, known for its sustainable, luxury casual suits, has teamed up with sizing technology leader Makip. Creating made-to-order, luxury casual suits for men and women,... View ArticleView Article

Charles Tyrwhitt announces the opening of its new store on Regent Street
Charles Tyrwhitt welcomes its 8th opening in just one year as it takes residency on London’s iconic Regent Street. The new store is in a beautiful... View ArticleView Article

Iconic apparel chain AllSaints opens at Silverburn
British fashion label AllSaints has joined the line-up at leading retail and leisure destination Silverburn, representing a fashion coup for the centre which has secured a... View ArticleView Article

Oliver Bonas to open largest store in Kent at Bluewater
Fashion brand Oliver Bonas will be opening its largest store in Kent at the Bluewater shopping centre this weekend. Spanning 3,272 square feet, the store will... View ArticleView Article

Passenger expands stateside with appointment of US general manager
Passenger, the responsible outdoor clothing company, is expanding stateside with the appointment of Matt Liddle as general manager for the US. In his new role, Liddle... View ArticleView Article

American Golf's "reset" leads to upswing in sales and profit
American Golf has said a reset has helped it to deliver an uplift in annual profit following the appointment of Nigel Oddy as chief executive a... View ArticleView Article

Iceland Foods chief to run London Marathon in memory of his mother
Iceland Foods executive chairman, Richard Walker, is to run in this weekend’s London Marathon as he looks to raise awareness and funds for Alzheimer’s Research UK.... View ArticleView Article

Uniqlo unveils third Oxford Street store
Uniqlo has opened a third store on London’s Oxford Street next to Tottenham Court Road tube station. With entrances on Oxford Street and Charing Cross Road,... View ArticleView Article

Laura Ashley returns to fashion
Laura Ashley is returning to fashion by launching a 47-piece collection this spring. Available at selected Next stores and on next.com, it will include a range... View ArticleView Article

Nisa Local store in Islington undergoes modern transformation
A Nisa Local store, operated by LA Foods, in Islington has undertaken a modern refurbishment, leading to a significant boost in customer footfall. The Islington store... View ArticleView Article

Pre-loved fashion pop-up returns to Westgate Oxford this May
Westgate Oxford will welcome back pre-loved fashion pop-up ‘we are.’ this May, with the fast-growing sustainable fashion business operating on Leiden Square over Friday 17th, Saturday... View ArticleView Article

Bensons for Beds appoints new Chief Commercial Officer
UK bed specialist, Bensons for Beds, has today announced the appointment of Mark Slater as Chief Commercial Officer. The role will see him become part of... View ArticleView Article

HR Strategies for Talent Management in the Retail Industry
In a modern, disruptive and competitive landscape, the combination of technology and HR strategies for talent management in the retail industry is absolutely crucial. This combination... View ArticleView Article

Making a Difference Locally teams up with Kellanova to support grassroots football
Nisa’s Making a Difference Locally (MADL) charity is launching an exciting new partnership with grocery brand Kellanova to support grassroots and inclusive football teams across the... View ArticleView Article

Tails.com becomes B Corp certified
Tails.com, the tailored dog food service, has become a certified B Corporation. Following an independent assessment by B Lab, the company achieved an overall score of... View ArticleView Article

YesColours launches Design Studio bolstered by new investment
Award-winning paint brand YesColours announces new strategic direction with Design Studio, backed by new investment strategy. “In April 2022, when we launched our innovative packaging for... View ArticleView Article

Dunelm posts third quarter sales growth
Dunelm has seen its third-quarter sales grow by 3% to £435 million despite the “challenging” homewares and furniture markets in which it operates. The retailer said... View ArticleView Article

BP invests in staff safety by rolling out body cameras to stores with higher levels of crime
BP has invested in the security of its retail teams by introducing body-worn cameras at stores experiencing higher levels of abuse and crime. The move is... View ArticleView Article

Crocs appoints Terence Reilly as EVP and president for Heydude
Crocs has appointed Terence Reilly as the incoming executive vice president and president of its Heydude footwear brand. Reilly most recently served as president of the... View ArticleView Article

H&M & Rokh celebrate new collaboration with event at Dover Street Market
H&M and Rokh have been celebrating their new collaboration with a crowd of industry insiders at London’s Dover Street Market this week. The event’s attendees included... View ArticleView Article

Trouva acquired by Fy!
Trouva has changed hands for the third time in two years after being acquired by Fy!, the AI-enabled marketplace specialising in home and living. In a... View ArticleView Article

Mint Velvet to join line-up at Centre:mk
Mint Velvet is to open its debut store at Centre:mk in Milton Keynes this summer as it continues its focus on expanding in premium retail destinations.... View ArticleView Article

Don’t ‘boil the ocean’ if you’re to make the most of AI, says Kingfisher leader
Successfully deploying Artificial Intelligence in retail will require businesses to focus on a handful of areas where the technology can really make a difference. That was... View ArticleView Article

Harvey Nichols appoints Julia Goddard as new Chief Executive
Harvey Nichols has announced the appointment of Julia Goddard as its new Chief Executive Officer, effective June 2024. Goddard succeeds Manju Malhotra, who served as CEO... View ArticleView Article

The Future of In-Store Technology: Embracing the Change
Retail is undergoing a ruthless renaissance after a transformation almost two decades long. The e-commerce eruption and pandemic lockdowns, as well as the customers’ inclination to... View ArticleView Article

IKEA opens first Irish distribution centre
IKEA UK & Ireland has opened its first ever logistics facility in Ireland. Marking a significant milestone in the furniture giant’s expansion in the country, the... View ArticleView Article

ProCook partners with Food Cycle charity
Kitchenware brand ProCook has announced a new partnership with Food Cycle, a UK charity that aims to alleviate food poverty, loneliness and food waste through community... View ArticleView Article

ASOS posts drop in sales as it works to become "faster, more agile and more profitable"
ASOS has reported that its adjusted first-half revenue declined by 18% to £1.5 billion, although the fashion retailer said it is making good progress on its... View ArticleView Article

B&M delivers 10% revenue growth
B&M has seen its full year sales rise by 10.1% to £5.5 billion as it continues its focus on delivering everyday low prices. In the 53... View ArticleView Article

ASOS appoints new chief financial officer
Online fashion retailer ASOS has appointed former Farfetch and Sainsbury’s executive Dave Murray as its new chief financial officer. Due to join the business on 29... View ArticleView Article

Matalan expands online offering with addition of 17 new third-party brands
Fashion and homewares retailer Matalan has significantly expanded its online offering by launching 17 new third-party brands across its core categories. It has also extended the... View ArticleView Article

Pangaia to open first standalone UK store
Materials science company Pangaia is to open its first standalone UK store in London’s Soho this summer The 1,500 square foot shop at 57 Carnaby Street... View ArticleView Article

JD Sports opens global flagship store at the heart of Champs-Élysées Paris
JD Sports has opened a global flagship store on the world-renowned Avenue des Champs-Élysées in Paris, with a grand opening to customers having taken place on... View ArticleView Article
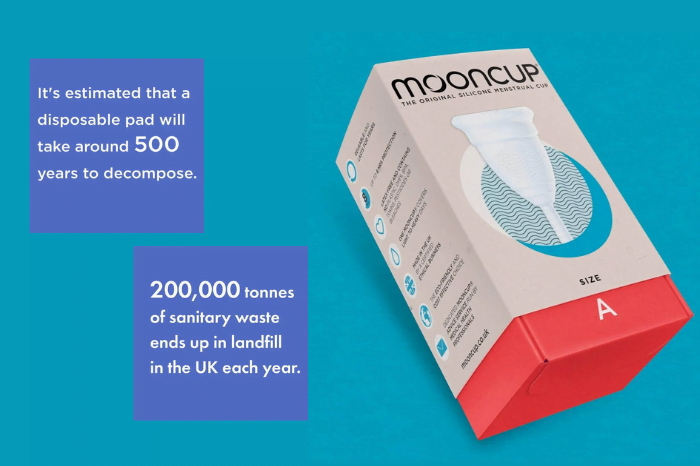
Mooncup launches in Holland & Barrett
Mooncup, the trailblazers in plastic-free menstrual products, have now launched at Holland & Barrett, a global leader in health and wellness retail. This marks a significant... View ArticleView Article

Dr. Martens to have new chief executive
Dr. Martens has announced that its chief executive Kenny Wilson has decided that this will be his final year with the footwear brand. Following a search... View ArticleView Article

Superdry announces restructuring plan
Superdry is launching a restructuring plan as it looks to ensure the survival of the struggling fashion business. This will include an equity raise, slashing rents... View ArticleView Article

Primark cuts prices on hundreds of kidswear items
Primark is cutting the prices of hundreds of children’s clothing and accessory items as part of a commitment to keeping prices low on kidswear. Prices have... View ArticleView Article

Charles Tyrwhitt expects business to grow by 20% over the next year
Menswear retailer Charles Tyrwhitt is expecting its business to grow by 20% over the next year as it benefits from an adjustment in its offering to... View ArticleView Article

Bath & Body Works opens first London standalone store
Bath & Body Works has chosen London’s Westfield shopping centre for the opening of its first London standalone store. Situated directly opposite Sephora at the White... View ArticleView Article

Margaret Dabbs London to open new clinic on King's Road
Beauty and wellness brand Margaret Dabbs is to open its seventh London clinic on King’s Road. Due to launch in May, the 824 square foot unit... View ArticleView Article

Lakrids by Bülow continues UK expansion with new store at Westfield London
Danish confectionery brand Lakrids by Bülow has launched a new store at Westfield London as part of its continued UK expansion. The news follows openings by... View ArticleView Article

The Perfume Shop unveils experiential new store in Ipswich
The Perfume Shop has had a scent-sational new addition as it opens the doors to another new and improved experiential store at Sailmakers Shopping Centre in... View ArticleView Article

Asda teams up with Pharmacy2U to launch online prescription service
Asda has become the first UK supermarket to launch an online prescription service. The retailer has teamed up with Pharmacy2U to launch the Asda Online Pharmacy... View ArticleView Article

Mango invests in shared mobility start-up Hoop Carpool
Mango is extending its innovation activities by investing in Hoop Carpool, a start-up that offers companies and universities a mobility alternative where employees and students can... View ArticleView Article

Cubitts to open first international store in the heart of New York City
Modern spectacle maker Cubitts has chosen New York’s SoHo for the launch of its first international store. Set to be the brand’s US flagship, the shop will open... View ArticleView Article

Trudon and Metal Morphosis to join line-up at Seven Dials
French candlemaker Trudon is set to open its first UK physical store at Covent Garden’s Seven Dials this June. Founded in 1643, the brand is the... View ArticleView Article

Kering appoints Stefano Cantino as the deputy chief executive of Gucci
Luxury group Kering has appointed former Louis Vuitton and Prada executive Stefano Cantino as the deputy chief executive of Gucci. Due to take up his role... View ArticleView Article

Healthy Pet Store hosts “stuff-a-thon” in aid of local dog shelters
A Southampton pet food retailer has teamed up with dog toy brand Kong to raise funds for local dog shelters through a ‘stuff-a-thon’ event. Healthy Pet... View ArticleView Article

Levi taps Burberry senior executive Gianluca Flore as new Chief Commercial Officer
Levi Strauss & Co. is pleased to announce the appointment of Gianluca Flore as the new Chief Commercial Officer and Executive Vice President, effective July 29,... View ArticleView Article

Charity Super.Mkt marks first anniversary with launch of concept stores at Brent Cross
The Charity Super.Mkt, a unique multi-charity department store, is back at Brent Cross to mark its one-year anniversary with the launch of two new and exciting... View ArticleView Article

Heather Lee Championing people excellence on the PiRA24 Judging Panel
We are excited to announce our latest judge for the People in Retail Awards 2024—Heather Lee. Returning for the second year, Heather brings a wealth of... View ArticleView Article

SPAR South West partners with FareShare to fight hunger in local communities
In the fight against food waste and hunger, SPAR South West’s primary distributor, Appleby Westward Ltd, has partnered with FareShare South West and Gregorys Logistics to... View ArticleView Article

Popeyes appoints director of acquisitions and estates
Popeyes has appointed Peter Gibson as director of acquisitions and estates. The news comes as the chicken QSR brand works to double its UK network of... View ArticleView Article

Majestic to expand into the Channel Islands
Majestic is to expand into the Channel Islands as it continues to invest in extending its physical store network. On 30 April, the specialist wine retailer... View ArticleView Article

Dr Hannah Shimko appointed as Director General of the GCVA
The Gift Card and Voucher Association (GCVA) has announced the appointment of Dr Hannah Shimko as its new Managing Director, effective April 10, 2024. Dr Shimko... View ArticleView Article

Tesco introduces ‘Best of British’ page on groceries website
Tesco has become the latest supermarket to launch a dedicated ‘Best of British’ page on its groceries website. The move will aim to make it easier... View ArticleView Article

White Stuff opens new store at McArthur Glen Outlet in Ashford
The White Stuff lifestyle clothing brand has opened a new outlet store at the McArthur Glen Designer Shopping Outlet in Kent’s Ashford. Situated close to M&S... View ArticleView Article

Ribble Cycles partners with Huub to launch new apparel
Ribble Cycles has collaborated with the premium endurance sport apparel brand Huub to launch a race kit for its new Ribble Rebellion race team. The team... View ArticleView Article
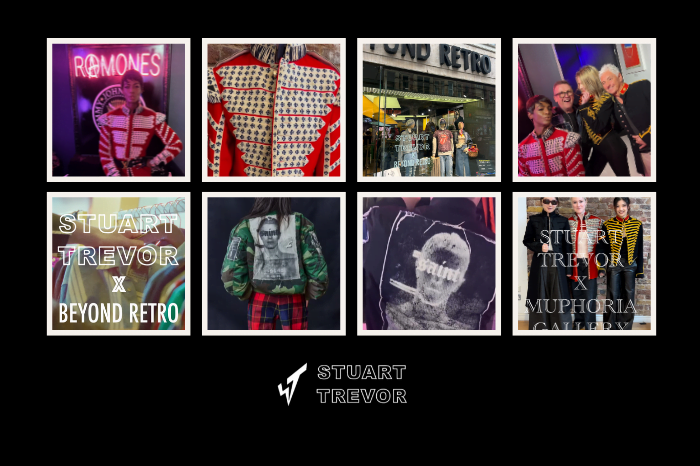
Stuart Trevor Collaborates with Beyond Retro and Muphoria for a sustainable style
Challenging the ‘norms’ of the fashion industry, Stuart Trevor, the founder behind the iconic brand All Saints, has collaborated with Beyond Retro and Muphoria Art Gallery,... View ArticleView Article

THE NEXT EVENT